As of April 2021, the execution of flash loans requires programming skills that are not easily accessible by the average layman.
Some truly smart programmers exploit vulnerable DeFi projects by launching a “flash loan attack” to manipulate the market in their favor.
Like taking an ordinary flash loan, a flash loan attack happens almost instantaneously thereby making it impossible for DeFi projects to fix their codes or counter against it in time.
DeFi has many different kinds of exploits but flash loan attacks are by far the most popular one because they allow near-unlimited capital without needing to put up security.
This makes them the cheapest to pull off and the easiest to get away with.
Page Contents
First… What Are Flash Loans?
I have written a detailed and easy-to-understand article on flash loans… if you have no idea how a flash loan works, click on the link below:
How Do Flash Loan Attacks Work?
A flash loan grants user the ability to borrow as much as they want without needing any upfront capital.
If you want $100,000 worth of DAI stablecoin, lending protocols such as Aave and dYdX will give it to you… nevertheless, this does not mean that the fund is yours.
In order to return the loan, you need to do something with the borrowed money, such as taking advantage of an arbitrage opportunity… (In other words, you cannot take the loan without doing anything with the funds)
If the opportunity is successful, the smart contract will automatically return the loans for you and you profit the remaining after interest which is usually set at 0.09%.
If the opportunity results in a loss, the transaction will simply reverse as though it never happened.
It sounds simple… except it is not.
The truth is, most flash loan attackers are good at math, excellent in programming skills, and have a good understanding of DeFi protocols which allows them to manipulate the market in their favor while still abiding by blockchain rules.
Why Are Flash Loan Attacks so Common in DeFi Protocols?
With flash loans, you only risk the transaction fees and not your entire portfolio, thereby making it a low-risk and high-reward endeavor for many hackers.
Three reasons why flash loan attacks are so common these days:
1. Flash Loan Attacks Do Not Require Huge Resources
Technically speaking, a hacker only needs an internet connection and a computer.
Of course, he/she needs to possess competency and intellectual acuity on blockchain technology to launch a successful flash loan attack.
A flash loan attack is extremely cheap in comparison to a 51% attack which requires huge capital and resources.
2. Flash Loan Attacks Are Incredibly Low Risk
Why would criminals want to rob a bank for a million dollars risking their lives or years in prison when they can simply pull off a flash loan attack in the comfort of their own homes?
It is true that in the past 2 years, hackers have shown us how easy it is to exploit vulnerable DeFi projects… but what is more interesting is how they get away with these attacks without any intervention from law enforcement whatsoever.
To date, NO flash loan attackers have been caught and punished.
3. Flash Loan Attacks Are Fast
No need to spend four months planning a heist in a classroom when a robber can simply go online and launch a flash loan attack that only takes a few seconds to execute.
Launching a successful flash loan attack does not require a great deal of time.
The low barriers to entry, low risk of getting caught, and tiny time investment are the main reasons why flash loan attacks are so predominant on DeFi today.
The 5 Biggest Flash Loan Attacks in 2021
1. PancakeBunny – $45 Million
| Audited by: | Haechi Audit (the audit film responded on 18 July 21, see below) |
| Date: | May 2021 |
| Damage: | $45,000,000 |
| Network: | Binance Smart Chain |
In May 2021, BSC PancakeBunny price went from $145 to $6 in an instance. Look at the chart below:

The attack consists of 8 flash loans to manipulate the price of several PancakeSwap pools that led to the minting of 697,000 BUNNY tokens which were sold away immediately.
For more information on PancakeBunny attack, read this and this.
2. Spartan Protocol – $30.5 Million
| Audited by: | Certik |
| Date: | May 2021 |
| Damage: | $30,500,000 |
| Network: | Binance Smart Chain |
The Flash loan attack on Spartan Protocol resulted in $30.5 Million lost.
This attack was made possible due to a flawed liquidity share calculation in the protocol where users burned their LP tokens in order to withdraw the underlying assets.
The hacker used a flash loan to inflate the asset balance of the pool before burning the pool tokens to claim a large number of underlying assets.
This results in $30.5 million loss in the affected pool.
For more information on this attack, read rekt and peckshield articles.
3. Popsicle Finance – $20 Million
| Audited by: | Peckshield |
| Date: | August 2021 |
| Damage: | $20,000,000 |
| Network: | Ethereum & BSC |
The attack on Popsicle Finance (Sorbetto Fragola) was made possible due to a simple bug which has inconsistent fee accounting when LP tokens are being transferred.
This is the breakdown of the attack:
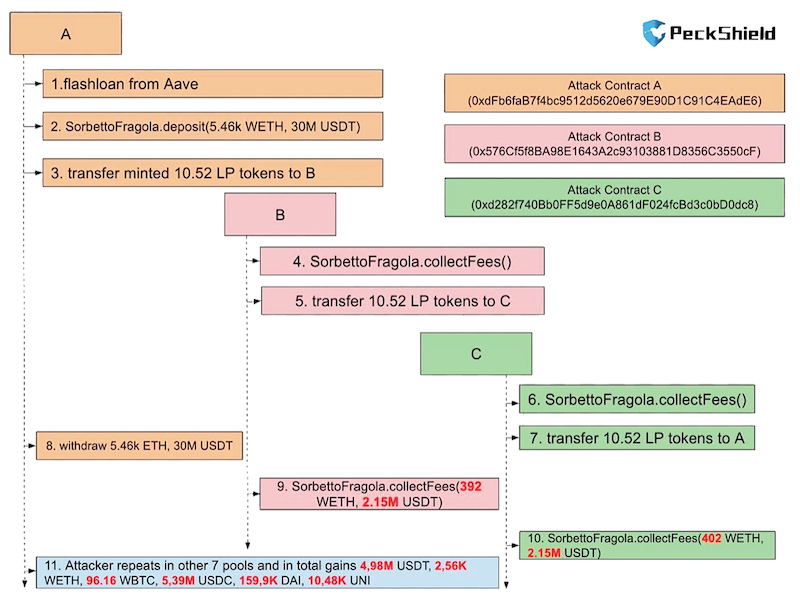
The simple bug found in the code is a tiny mistake that could easily be detected and removed during the auditing phase.
Everyone makes mistake but not everyone makes a mistake that cost $20,000,000 in TVL.
Blockchain auditors need to step up their game to be stricter and more thorough in their checks.
Millions of dollars were lost and Peckshield is still chasing a ghost on Twitter.
4. Cream Finance – $18.8 Million
| Audited by: | Trail of Bits (before the AMP collateral tokens came into effect) |
| Date: | August 2021 |
| Damage: | $18,800,000 |
| Network: | Ethereum |
Trail of Bits is an auditing powerhouse which does not compromise on security. They are one of the very few auditors that were not mentioned on the leadership board on Rekt.news.
Nevertheless, with a change of code or protocol, even the most trustworthy and robust audit becomes irrelevant.
A loophole opens up for hackers to exploit when Cream Proposal decided to add AMP token as a collateral asset on 10 February 2021.
For the full details of the exploit, read this.
How to Prevent a Flash Loan Attack from Happening
The truth is, having smart contract audits is NOT enough to prevent attacks and exploits.
Projects need to do more to shield against hackers and attackers. Below are some solutions worth noting:
1. Internt Insurance Fund
Projects such as Maker and Aave have decided to use their native tokens as the risk backdrop:
- Maker minted MKR to cover for liquidation shortfall in DAI
- Aave rolled out stAAVE to cover potential shortfall for the depositors
2. Insurance
Projects such as Unslashed Finance offered protocol-level covers to Lido and Paraswap. This gives protocols the opportunity to buy insurance covers for their users/depositors.
3. Bug Bounty
Bug bounty projects like Immunefi encourages hackers to find bugs in protocols in exchange for handsome rewards rather than exploiting them. The biggest reward to date is $1.5 Million.
A bug bounty program cannot stop exploitation. But what it can do is encourage hackers to do the right thing by giving them a choice.
4. Industry-wide Insurance Pool
Industry-wide insurance pool is an idea similar to the Federal Deposit Insurance Corporation (FDIC) where everyone in the industry participates by paying a fixed fee or parts of their earnings to the pool.
When one of the participants experiences a hack, a claim can be taken from the pool to reimburse the damage caused by the hack.
I know this idea seems a little farfetched especially at this early stage of DeFi but I think it is still worth mentioning nonetheless.
5. Hold Auditors Accountable
Blockchain auditors such as Hacken and Certiks should be held accountable for exploits too.
Auditors can have their skin in the game by staking on DeFi alternative insurance platforms such as Nexus Mutual.
Whenever the audited protocols are hacked, auditors themselves will experience a loss too.
This can pressure the auditors to perform stricter auditing and tougher security checks for their clients.
Flash Loan is a Double-edged Sword
On the bright side, a flash loan is a remarkably innovative technology that makes use of smart contracts to bring convenience and novelty to the DeFi ecosystem.
On the other hand, hackers can leverage flash loans to attack vulnerable projects on the blockchain with no capital… as a result, these attacks usually bring in huge profits for the hackers.
Like all tools, flash loans can be used for good and bad purposes.
Conclusion
From what we have seen so far, flash loan attacks have strengthened the whole DeFi ecosystem.
Many projects have now taken the time to work on their codes and build a solid infrastructure to prevent these attacks from happening.
As flash loans are still at a nascent stage, the attacks can be seen as a silver lining that mitigates the kinks in the DeFi ecosystem and makes it more antifragile.